New Delhi, Sep 25, 2019-
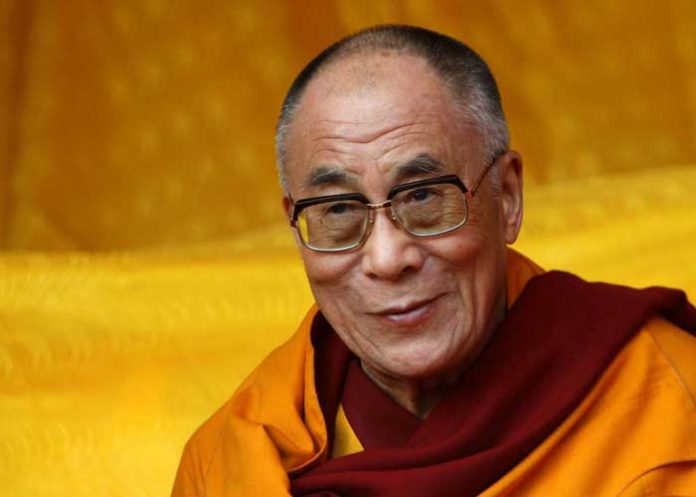
Sophisticated Chinese hackers posing as NGO workers, journalists and tourists to India have targeted senior members of Tibetan groups close to the Dalai Lama, installing spyware on iPhones and Android devices via malicious links in WhatsApp text exchanges with them.
In a detailed report, Canada-based Citizen Lab at the University of Toronto revealed that the same group of hackers earlier targeted the Uyghur Muslim community in China.
The researchers observed 15 intrusion attempts against individuals from the private office of the Dalai Lama, the Central Tibetan Administration, the Tibetan Parliament and Tibetan human rights groups in November 2018.
“On April 22 and May 21, 2019, we observed two additional attempts. The majority of people who were targeted hold senior positions in their respective organizations and the malicious links required only a single click on a mobile device to work,” the report said on Tuesday.
The Citizen Lab observed that the Chinese group named Poison Carp employed eight Android browser exploits and one Android spyware kit, as well as one iOS exploit chain and iOS spyware, to attack Tibetan groups.
“This campaign is the first documented case of one-click mobile exploits used to target Tibetan groups, and reflects an escalation in the sophistication of digital espionage threats targeting the community,” said the research team.
“Beyond the technical overlap in these campaigns is the fact that they all targeted ethnic minority groups related to China: Uyghurs and Tibetans,” they added.
The Tibetan community has been besieged by digital espionage for over a decade.
To address such challenges, Tibetan groups recently formed the Tibetan Computer Emergency Readiness Team (TibCERT), a coalition between Tibetan organisations to improve digital security through incident response collaboration and data sharing.
In November 2018, TibCERT was notified of suspicious WhatsApp messages sent to senior members of Tibetan groups.
“With the consent of the targeted groups, TibCERT shared samples of these messages with Citizen Lab. Our analysis found that the messages included links designed to exploit and install spyware on iPhone and Android devices,” said the researchers.
On November 13, 2018, a senior staff member at a Tibetan human rights group was contacted on WhatsApp from a previously unknown number.
The persona claimed to be “Jason Wu”, head of the “Refugee Group” at Amnesty International’s Hong Kong branch.
There does not appear to be any “Jason Wu” currently employed by Amnesty International.
Once the pretext was established, the operator shared a link shortened with bit.ly that redirected to a page that contained an iOS exploit.
In another intrusion attempt, a staff member from the same Tibetan human rights organization was contacted by “Lucy Leung”, a person masquerading as a New York Times reporter seeking an interview. The operator again shared a malicious link.
The intrusion attempts arrived via WhatsApp messages from seven fake personas designed to appear as journalists, staff at international advocacy organisations, volunteers to Tibetan human rights groups, and tourists to India.
“The fake personas exclusively used WhatsApp phone numbers with Hong Kong country codes (+852),” said the report.
The iOS exploit and spyware were earlier used in watering hole attacks reported by Google Project Zero.
A Volexity report earlier this month also published details of an espionage campaign against Uyghurs that used compromised websites to infect targets with Android malware.
“The level of threat posed by Poison Carp and the linked campaigns are a game changer. These campaigns are the first documented cases of iOS exploits and spyware being used against these communities,” the research noted. (Agency)